Knowledge base
1000 FAQs, 500 tutorials and instructional videos. Here, there are only solutions!
Cancel an automatic vulnerability scan correction
This guide explains how to apply or cancel a patch, quarantine, or block performed by the vulnerability detection tool, the free and complementary antivirus protection that automatically protects Web Hostings against malware and security vulnerabilities.
Preamble
- The tool automatically corrects detected vulnerabilities within 7 days without any action on your part.
- It is strongly discouraged to cancel a patch or quarantine unless you are sure of what you are doing.
Apply or cancel a correction
To do this:
- Click here to access the management of your hosting on the Infomaniak Manager (need help?).
- Click directly on the name assigned to the hosting concerned:
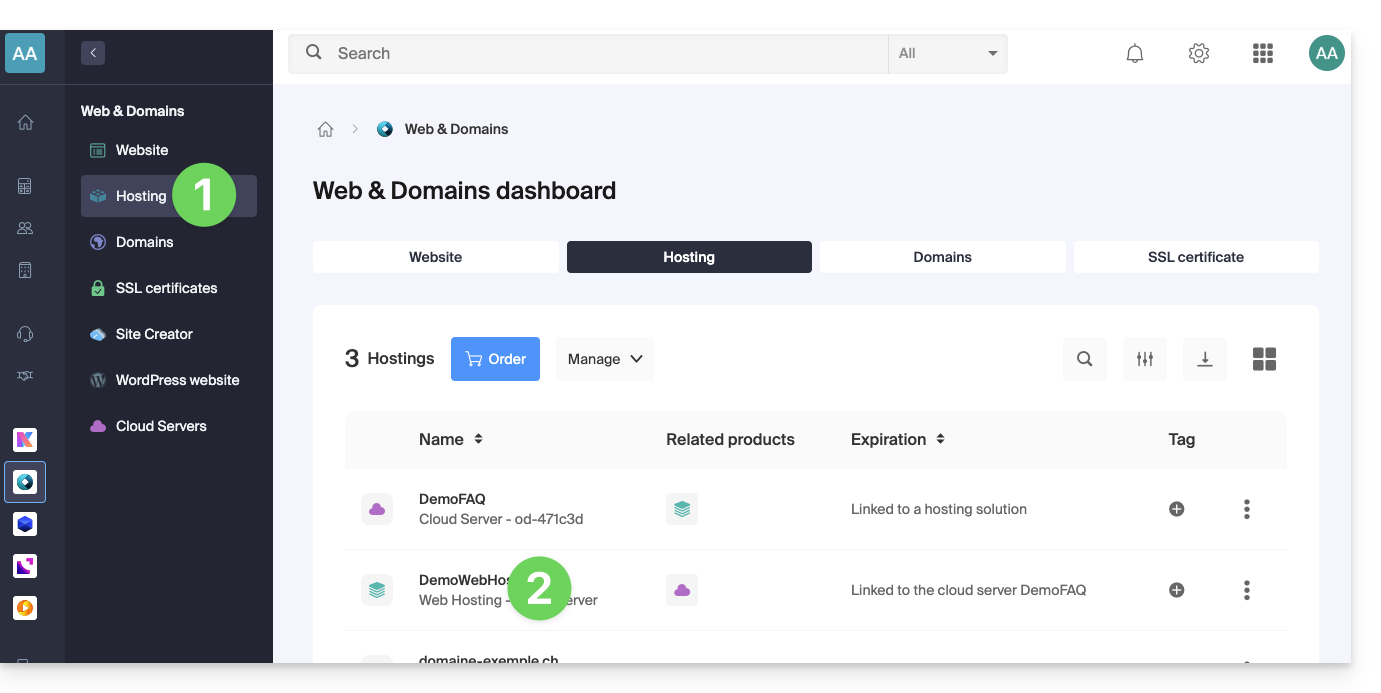
- Click on Security in the left sidebar.
- Click on Vulnerability scan in the left sidebar:
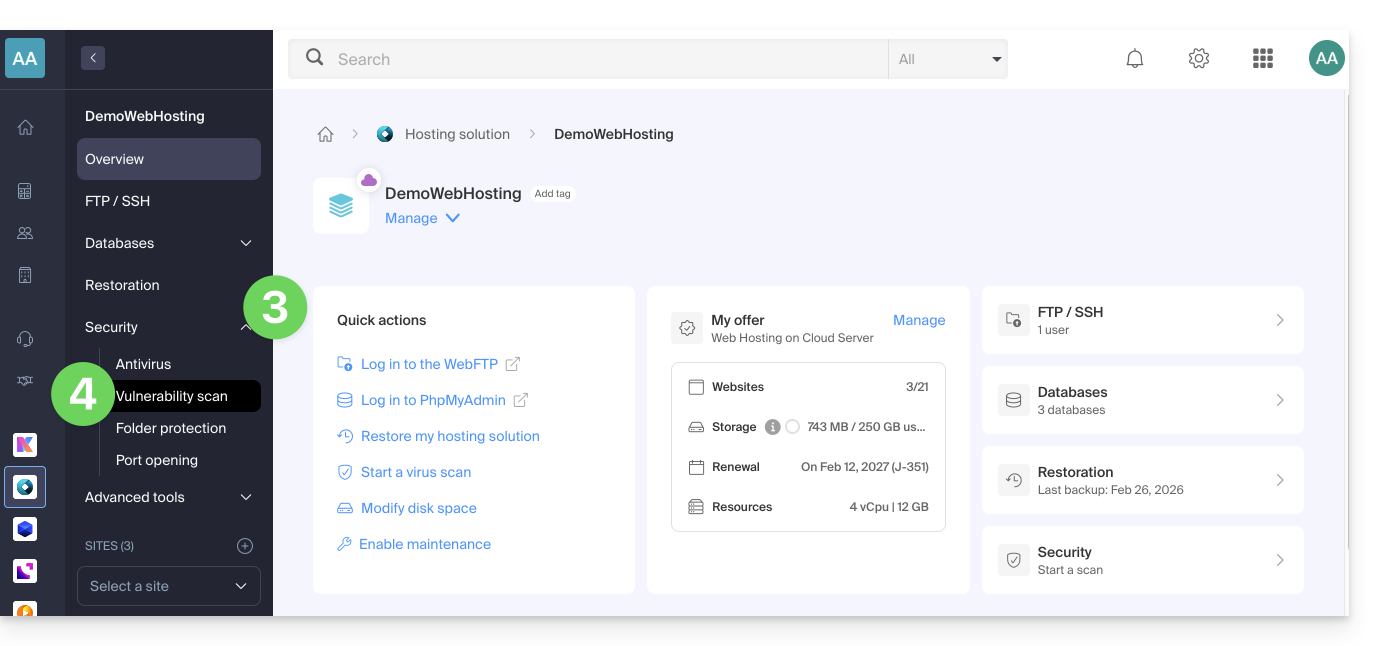
- If nothing specific is displayed, first click on the button to View history.
- If there is an event history, click on the action menu ⋮ to the right of the vulnerability concerned in the displayed table.
- Click on Cancel correction.
- In some cases, other actions are possible:
- Apply the patch: immediately corrects the vulnerability.
- Cancel the patch: cancels the correction and restores the original vulnerable file (not recommended).
- Delete the file: permanently removes the malware from your hosting (may affect the functioning of your site).
- Quarantine: isolates the vulnerable file and allows you to restore it if needed (may affect the functioning of your site).
- Cancel quarantine: restores the isolated file to its original location (not recommended).
- Add an exception: allows you to indicate to the tool that the vulnerable file is safe; it will no longer be analyzed.
- Delete an exception : deletes the Allowed status of the file; the latter will be reanalyzed.
Details of the different statuses
- VULNERABLE : a vulnerability has been detected in a file; the path column indicates the location of the file.
- RESOLVED : the vulnerability has been fixed by the tool.
- ALLOWED : the vulnerable file has been manually allowed; the latter will no longer be analyzed by the tool.
- RESOLVED : a manual correction outside the tool has been applied to the file (CMS update, source code modification, manual file deletion, etc.).
- FIX REVERTED : the tool's fix has been manually reverted; it is possible to reapply the patch.
Link to this FAQ:
Has this FAQ been helpful?