Knowledge base
1000 FAQs, 500 tutorials and instructional videos. Here, there are only solutions!
Discover the vulnerability detection tool
This guide presents the vulnerability detection tool for your Web Hosting.
Preamble
- There are thousands of cyber threats, and if your website were to be infected, your business could suffer, not only due to its unavailability, but also due to the loss of trust from your visitors and customers.
- The tool offered by Infomaniak is a free and complementary protection to the antivirus that protects all Infomaniak hostings against malware and security vulnerabilities.
- Infomaniak ensures the protection of hostings by analyzing exclusively the folders of the sites (webroot); outside of this, no synchronous scan is performed on the rest of the hosting.
Operation of this service
The tool works in the background to detect potential security issues. These vulnerabilities can allow malicious individuals to alter the content of your sites, which could harm your reputation with your customers and search engines.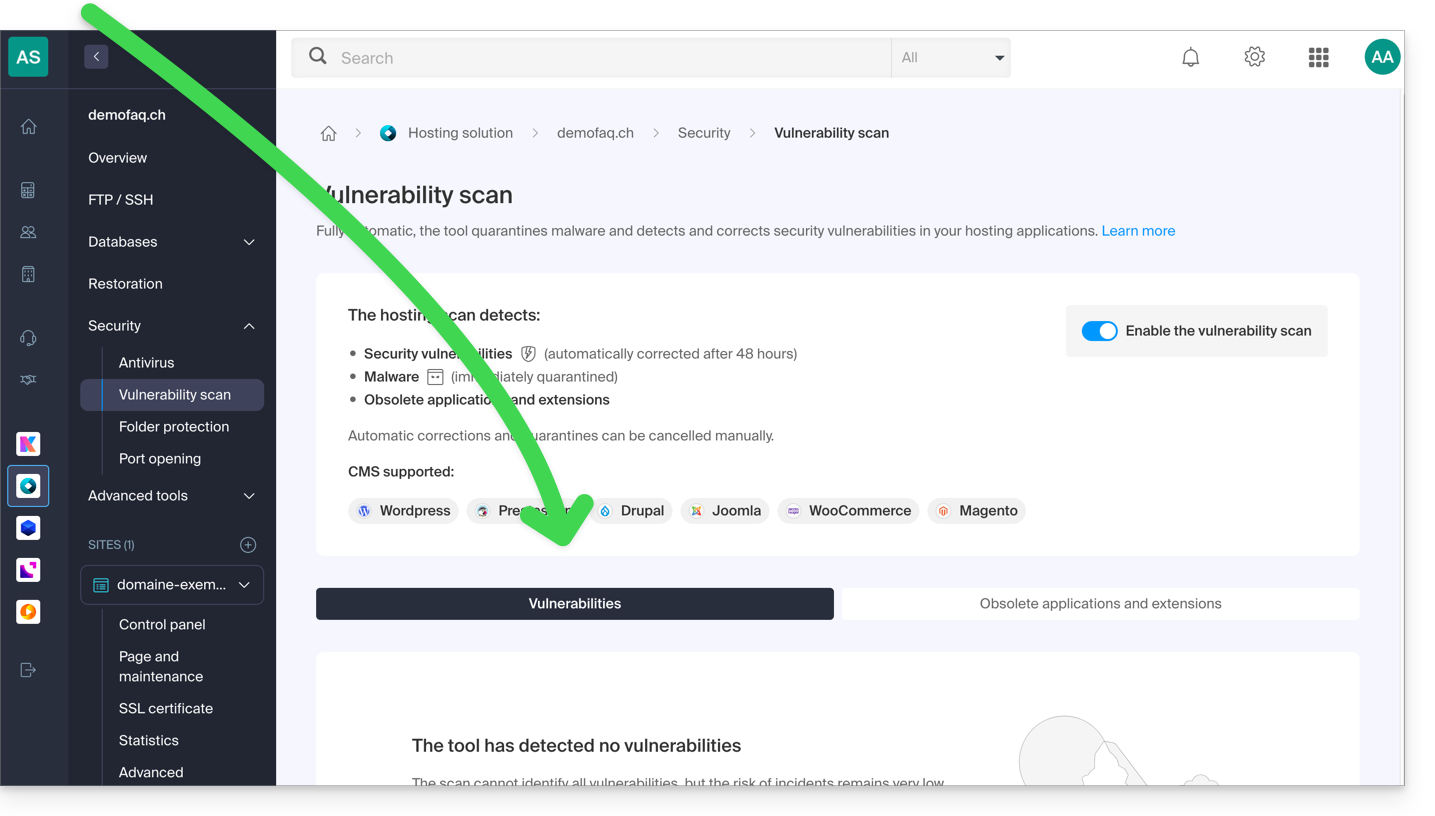
Without any action on your part within 48 hours following detection, the tool automatically corrects the security vulnerabilities of the majority of CMS and/or quarantines malicious software, without affecting the proper functioning of your sites.
If necessary, you can:
Following a detection, it is recommended to check your entire hosting, especially if you notice suspicious modifications that the protection would not have detected automatically.
A second tab allows you to analyze and display obsolete applications and extensions on your hosting: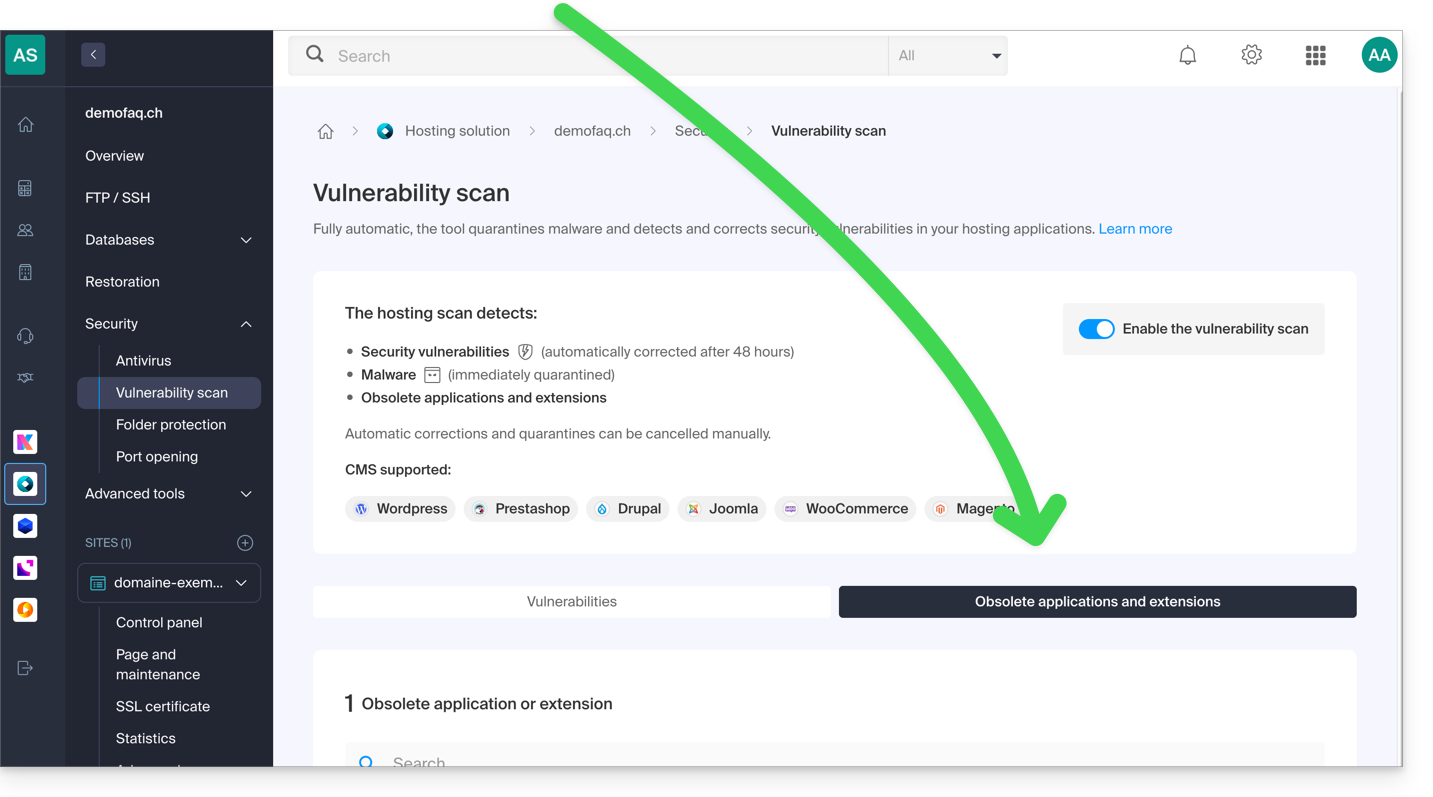
Data confidentiality
Like Infomaniak, the tool is compliant with the General Data Protection Regulation (GDPR) of the European Union: the analyses are performed locally on Infomaniak's servers. The content or signatures of the scanned files are not transmitted outside the infrastructures.
In accordance with the privacy policy, the data processed is limited to the strict minimum and concerns the username, email address, path, and name of the files, primarily in order to communicate the detections to the customer.
Link to this FAQ: https://faq.infomaniak.com/2326
Has this FAQ been helpful?